Get exclusive insights that set you apart from competitors.

AudienceSCAN® psychographics and buyer personas
With extensive profiles of over 1,355 customer groups, AdMall's exclusive AudienceSCAN research provides unparalleled insights into consumer behavior, purchase intent, digital and technology usage, health and wellness concerns, automotive preferences, leisure interests, dining habits, and more.
Whether you're a business development specialist seeking new opportunities or a marketer aiming to win over your ideal customer, AudienceSCAN empowers you to make data-driven decisions. By reaching the people who truly matter and crafting messages that resonate, you can maximize your marketing efforts and drive conversions like never before.
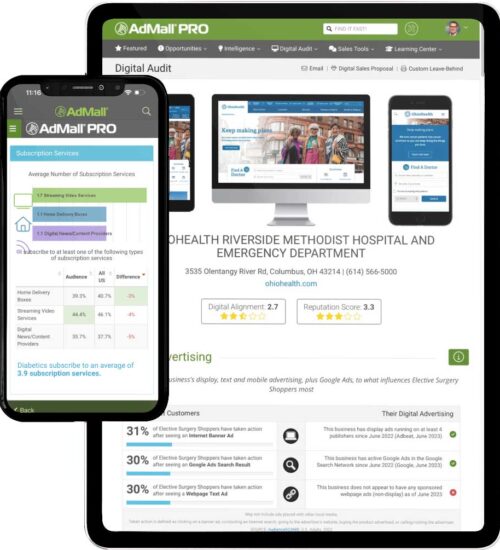
Digital Audit™ digital marketing analysis in seconds
AdMall’s Digital Audit does in 60 seconds what would take you 60 minutes to do by hand. This exclusive tool conducts a real-time data capture of any client or prospect’s digital presence and reveals where their digital marketing is falling short.
Using real-time big data, Digital Audit analyzes the account’s advertising, marketing activity, reputation and findability. It then helps them to meet their customer's where they are online — comparing their activity to the pre-purchase research methods used most by customers who intend to buy what they’re selling in the next 12 months. It's also an excellent competitive intelligence tool!


Latest B2B buyer research from SalesFuel
Uncover invaluable insights with SalesFuel's exclusive B2B buyer research. Gain a competitive edge with the latest studies like: Voice of the B2B Buyer, Voice of Health Care Marketers, State of Media Sales, Voice of the Sales Manager, and Voice of the Sales Rep.
Unleash the power of data-driven decision making, fine-tune your strategies, and confidently stay ahead of the competition. Elevate your marketing endeavors with SalesFuel's authoritative research, empowering you to achieve remarkable results.
Category analysis, trends, and benchmarks for 400+ verticals
Unlock the key to more effective campaigns with AdMall's unparalleled business intelligence. Our platform provides you with the insights necessary to create targeted, impactful campaigns that resonate with your audience.
From market-specific data to expert analysis across various verticals, AdMall empowers you to make data-driven decisions and optimize your strategies. Whether you're refining your messaging, identifying new opportunities, or fine-tuning your targeting, AdMall equips you with the tools to build campaigns that drive exceptional results.

Our clients include agencies of nearly every type and size across the U.S.
Provide Relevant Value™
at every meeting with AdMall.
- Get smart, fast with AdMall's exclusive Digital Audit with curated data from multiple platforms all in one place
- Get the a‑ha moment needed to win your next big account with AdMall's category research and analysis
- Know your client's customer using proprietary AudienceSCAN customer profiles
- Keep current accounts engaged using AdMall for better pre-call preparation and needs analysis
- Expand marketing budgets with co-op advertising and trade marketing funds
- Access insights from anywhere within seconds with the AdMall mobile app
Grow your agency's billings with
3 types of intelligence from AdMall.
SALES INTELLIGENCE
AdMall builds sales credibility so your new business hunters can be seen as trusted advisors that generate leads for future clients
MARKETING INTELLIGENCE
AdMall is the most trusted local market research and market intelligence tool for media companies and small-to-midsize agencies in the United States
BUSINESS INTELLIGENCE
AdMall delivers pre-sales research and digital marketing intelligence for understanding B2C, B2B, and franchise businesses







